

Right to repair isn’t a new topic but it’s growing in momentum. In the last decade, it’s proven to be an impasse large between manufacturers and consumers who demand the opportunity to repair their vehicles haven’t been able to overcome.
Why? Because the right to repair isn’t easily addressed. In fact, there are several important issues that the right to repair movement raises. How did this all begin?
It started with agriculture equipment
Farming equipment isn’t what it used to be. A few decades ago, a brokedown tractor could be fixed on site with tools and parts a farmer had on hand. Today, that’s just not possible. As agriculture evolves, so too does the machinery used. Tractors that have broken down can’t be fixed without diagnostic software to pinpoint bugs or issues that cause equipment to malfunction. Instead, farmers must pay hefty call-out fees, something that just doesn’t sit well with them.
To address this practice, eight farming states backed a bill to pass “right to repair” legislation back in 2012, which today, seems closer to possible than ever before. The federal government is taking steps towards their own bill with the Senate’s The Agricultural Right to Repair Act going around capitol hill.
Right to repair, by all means, sounds fair. The consequences, however, are often not clearly explored. Let’s start with modern vehicles.
What’s under a modern hood?
The average car has between 60 and 150 electronic control units or ECUs that have replaced the traditional mechanics of cars from just a couple of short decades ago. There’s one for the air intake of your engine, air conditioning system, another for your braking systems, one for your lights, one to control your radar and external sensors, an ECU for your infotainment system, and the list goes on.
These ECUs are responsible for translating your actions into electronic commands that your car performs. Take accelerating: you put your foot on the pedal and command travels from your pedal’s sensor to the engine’s ECU and then to your engine to increase speed in an optimal manner. As this happens, the ECU uses a micro electromagnetic sensor (MEMS) to measure the acceleration/velocity of your car, along with a dedicated signal conditioning unit, data converter, and fuel control unit.
It’s these intricate systems that OEMs are trying to protect.
Sure, IP is definitely sensitive, but more alarming is the risk of exposing the very systems that keep vehicles safe and secure when parked and on the road.
To show just how vulnerable a connected car can be, we hacked a telematics server and gained access to a new vehicle. In just a few commands, our security researcher was able to lock the owner out of the vehicle, activated her horn while she was driving, turned side mirrors in and out, and much more.
The security risks lurking in the deep and dark web
More people, including those with no cybersecurity or electronics experience, are trying to gain access to diagnostic software and tools to repair their vehicles without going through the OEM. For the first time, they are attempting to hack into their own vehicles in order to repair parts and address various software hurdles.
Unfortunately, there is no beginner’s luck here. The deep and dark web is a large and untamed ecosystem people turn to, looking for free, ‘cracked’ versions of software.
Tuners and enthusiasts may think they’ve struck gold by downloading what they need from suspicious or seemingly safe-looking websites or forums. They may also think they’ve saved time and money on potentially costly manufacturer repairs, but they unwittingly expose themselves to untrustworthy software from unknown and potentially malicious sources.
Using untrustworthy software and hacking cars for self-repair can result in voided warranties, installation of malware, spyware, ransomware, and more.
Vehicle hacking threats are real
Upstream’s team of automotive-specific analysts scour the deep and dark web, using automatic engines and various tools to identify malicious actors that look to collude across automotive and cyber forums.
Our analysts found a 253% spike in vehicle hacking chatter in 2021 compared to the previous year, leading to more sophisticated attacks and putting driver’s personal information at risk of reaching the black market. This information can be sold for as little as $10, all the way up to thousands of dollars depending on multiple factors.
Last year, attempts by farmers to self-repair their agriculture equipment opened the door to multiple vulnerabilities. Hackers were able to access data of all customers who purchased vehicles from two different manufacturers by convincing them to unknowingly install malware on their vehicles. The data collected by the hackers via malware was later found to have been shared on the dark web.
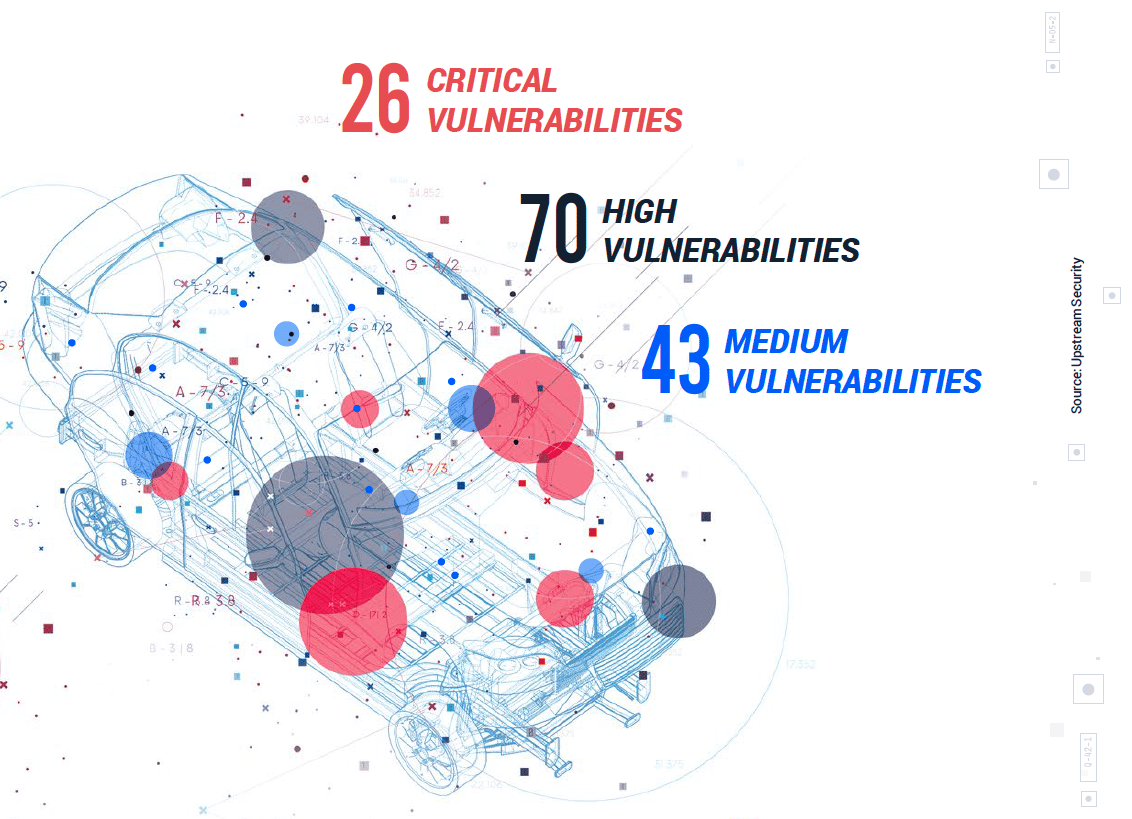
Instances like these aren’t typically the cause of just one vulnerability either. We identified 26 critical, 70 high, and 43 medium CVSS-scored vulnerabilities in 2021.
Using hacked software also presents a safety risk. As hackers gain access to a vehicle’s system, they are able to perform any number of attacks. In 2021 alone, 84.5% of attacks were carried out remotely compared to 51.5% that took place from a short distance.
Your insurance policy could be affected
Insurance providers are gearing up to meet the new wave of connected vehicles. With more data on telementics, they can better assign risk. Connected vehicles could soon offer integrations with insurer platforms for instant telematics data. While this could be considered a step towards more accurate insurance premiums, this advancement raises cybersecurity concerns regarding the collecting, anonymization, and storing of this first-party data.
Connected cars are magnets for cybersecurity threats, and with 49.3% more connected cars on the road, a hacked vehicle could expose an insurer’s IT networks to a cyber attack. This means your policy could get a premium bump as cybersecurity proves hard to control.
Where does the industry go from here?
There isn’t a simple solution to the drive for self-repair but there may be ways to forego some of the cybersecurity risks of hacking into one’s own vehicle.
Before picking a path, OEMs must gather enough data to make an informed decision. They’ll need to take a dive deep into attack vectors, trends, and emerging practices that threaten their servers, assets, and operator safety. That’s why our 2022 Global Automotive Cybersecurity Report offers a closer look at trends, threats, attack vectors, regulations, standards, and more. It paints a clearer picture of the state of automotive cybersecurity today.

