Runtime AI and API Security
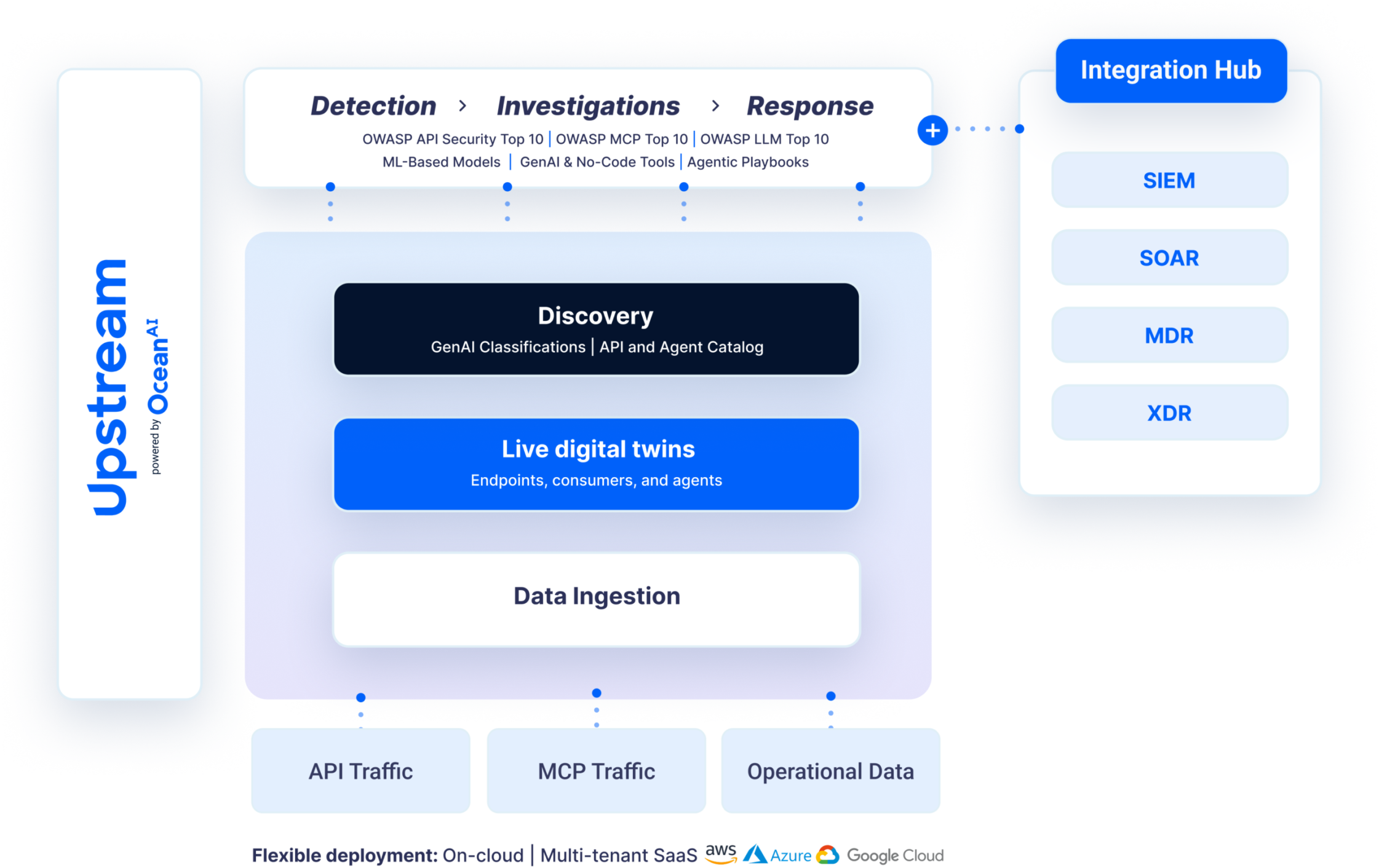
Helping security teams to discover AI agents and API traffic, monitor their intent and behavior, detect real-time threats, and automating investigations.
Request a Demo
Contextual and stateful detection, analyzing AI agents and API traffic alongside operational data streams to protect the full data-to-action pipeline
Upstream’s live digital twins maintain a historical and behavioral representation of assets, endpoints, consumers, and agents.
The platform monitors all traffic and provides a stateful analysis across the entire ecosystem, supporting a more comprehensive and resilient cybersecurity posture.
Built for Massive Scale and Complex Environments
The platform ingests and analyzes billions of monthly API transactions and MCP traffic within flexible SaaS or customer cloud deployments to meet PII and regulatory requirements.
Advanced API and AI Agent Discovery and Behavior Profiling
Upstream offers comprehensive discovery tools for API endpoints, consumers and agents to ensure full coverage. The platform also profiles assets over time for deep contextual analysis.
Stateful Threat Detection Across a Sequence of Actions
Live digital twins build stateful models of endpoint, consumer, and agent behavior, powering ML-based threat detection that infers attack sequence and intent across the full execution flow.
Threat Hunting, Investigations and Response
Ocean AI, Upstream's AI layer, delivers LLM-powered security workflows for low-and-slow or unknown risks, enabling teams to query data, extract insights, triage, and build agentic workflows.
Automated discovery and catalog
Identify, classify, and understand all API and MCP traffic.
Upstream builds and maintains a comprehensive API and agent inventory by ingesting traffic and logs to uncover undocumented tools, shadow servers, and zombie resources, as well as prompt and context. Using AI-powered classification, the platform maintains a live catalog of functional relationships, sensitive data exposure, and high-risk surfaces.
ML-based detection
Apply stateful, ML-driven behavioral context to surface known and unknown threats.
Using the live digital twin and Ocean AI, Upstream applies stateful, ML-driven behavioral analysis to detect anomalies and attack patterns. By correlating API transactions and MCP traffic with inferred intent and behavioral baselines for endpoints, parameters, consumers, and agents, the platform evaluates request, response, and authentication behavior over time and identifies anomalies, misuse, or sequential activity indicative of distributed or low-and-slow attack chains. Coverage includes OWASP API Security Top 10, OWASP MCP and LLM Top 10, misconfigurations, business-logic abuse, enumeration, and fraud attempts, with additional flexibility provided through a no-code detection builder for customer-specific logic.
GenAI-powered investigations and threat hunting
Reconstruct events and understand impact with contextual correlation with natural language querying.
Upstream provides full transaction history and cross-asset correlation to trace events across APIs and MCP servers. IIntent and behavioral baselines agent-to-tool interaction chains, and live digital twin signals reconstruct event chains, including prompt injections, to validate anomalies and power proactive threat hunting. Ocean AI supports investigations through GenAI-driven summaries, data classification, alert interpretation, insights, and querying to help teams rapidly determine impact and remediation.
Effective response and agentic remediation
Coordinate remediation through integrated workflows and automated actions.
Upstream connects with SIEM, SOAR, WAFs, API gateways, and other enterprise systems to support automated or analyst-driven remediation. Actions can include blocking or isolating API consumers, MCP servers, or non-human agent identities, revoking tokens, adjusting rate limits or policies, and sending enriched alerts to external systems.
API Security Frequently Asked Questions
AI and API security are all about context, and often risks can only be detected when analyzing sequences of actions and correlating them with the impact or consequences. Upstream provides the necessary context and continuity across the full execution flow to prevent malicious operations that appear benign when viewed as disconnected steps.
A typical WAF is stateless and examines transactions one by one. Upstream uses proprietary live digital twin technology to build a stateful, contextual analysis of endpoint and consumer behavior. This allows the platform to detect complex, low and slow attack chains that look like legitimate traffic to a standard WAF.
Foundational visibility is the core of our platform. Upstream automatically constructs a comprehensive API inventory by ingesting traffic, documentation, and operational logs. This process uncovers all active endpoints, including undocumented, shadow, and zombie APIs. It continuously updates the catalog to classify data exposure and functional relationships.
Upstream monitors AI agents in real-time to ensure their actions are safe and secure. By tracking relationships between agents and their physical impact, the platform detects deviations like prompt injections that alter system behavior.
Yes. Beyond an extensive and pre-configured set of detectors, all of which are customizable to meet specific requirements, the platform includes a no-code and GenAI-powered detector builder. This allows your team to create tailor-made detectors for unique business logic, misuse attempts, or operational risks without writing a single line of code.
No. Upstream is designed as a cloud-native solution with a zero latency impact. The platform typically ingests data via traffic mirroring from your gateway, load balancer, or a lightweight agent. This ensures your critical applications remain fast and responsive while under full security monitoring.
Ocean AI offers purpose-built GenAI and Agentic AI tools to streamline investigations. Analysts can use natural language querying to reconstruct event chains and understand the root cause of an anomaly quickly. It provides GenAI-driven summaries and alert interpretations, helping your team determine the scope and impact of threats at scale.
We offer flexible deployment to meet your specific regulatory and PII requirements. You can choose a multi-tenant SaaS model or deploy directly within your own private cloud environment. The architecture is built for massive scale and can process billions of monthly API transactions across various infrastructures.
More to dig into
Impact of PCI DSS on API Security For Mobility Products, Apps, and Services
Read more

Beyond the Cyber Resilience Act: Building Holistic Cyber Resilience
Read more
Live Digital Twins Power Dynamic and Multi-Dimensional Anomaly and Risk Detection
Read more
Upstream Safeguards Autonomous Vehicle Technology with May Mobility
Read more
Ford Trucks Collaborates with Upstream Security to Protect Its Connected Vehicles Against Cybersecurity Risks
Read more
Fifty Robotaxis, One Dead End: A Real-World Stress Test for Mobility API Resilience
Read more
APIs in the Driver’s Seat: AI Agents and the Future of Automotive Cybersecurity
Read more
