

Car manufacturers and managed fleets use a wealth of data to gain visibility into their connected cars and fleets. Smart use of telematics data, which is usually sent from the vehicle to a back-end telematics server, can improve safety and business efficiency as well as enable new services, maintain assets, reduce costs and liabilities, improve customer service and ultimately drive competitive advantage.
However, telematics servers don’t only collect data. They can also send remote commands to the car including: updating car software remotely, turning the engine on or off, locking and unlocking doors and many others.
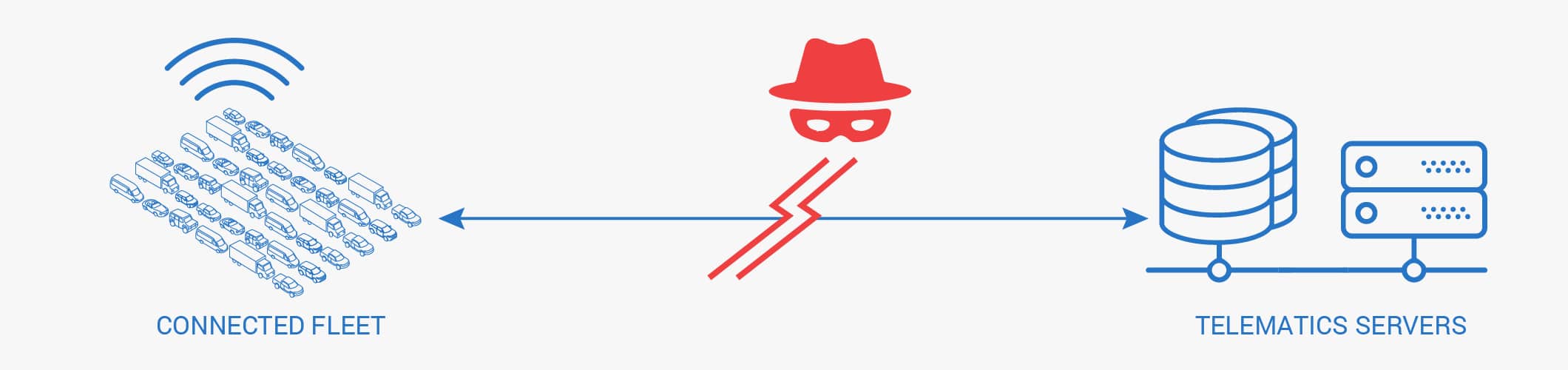
It goes without saying that as telematics systems become part of the connected car ecosystem, if not properly secured they could be exploited by hackers for a wide range of purposes, with worrying implications for both the business and driver and passenger safety.
If hackers gain access to the telematics’ private network and impersonate the command and control server via one of the fleet vehicle’s attack surfaces: e.g. Wi-Fi, Bluetooth or SIM etc., they could potentially reach multiple vehicles within the fleet, inject remote commands to the vehicles, cut their lifeline communication to the real back-end server and even cut off an entire fleet’s communication. Injecting telematics commands into the fleet’s telematics communication channel could enable the hacker to:
- Remotely re-configure the vehicles Telematics Control Unit (TCU) to stop communications
- Send a “disconnect from carrier” command to vehicles to disconnect them from the cellular network
- Infect the fleet’s vehicles with malicious software
Imagine a ransomware attack on a connected fleet where hackers cut off all server-to-fleet communication, demanding ransom to resume services. For the hacker, such a ransomware attack on taxi mobility providers, on-demand services, car rental and car sharing firms and a range of commercial enterprises could be worth vast sums of money.
For the fleet’s operation, this kind of server impersonation hack could result in
- No remote command and control communication to vehicles
- No OTA software updates
- No data from vehicles
- No route planning
- No data services
- No location data
- No emergency services
For these mega businesses, this type of hack could result in potential serious long-term damage to their reputation and profits.

What needs to be done?
One way to secure the telematics channel is to use an encrypted VPN from the vehicle to the back-end server. However, implementing a VPN client on the vehicle side requires the installation of new software or hardware components into the vehicles themselves. To do this, close collaboration with OEMs throughout the entire design and production cycles would be required. These cycles take years to complete so they do not address the vulnerabilities of the millions of cars and fleets currently in production or already on the road.
Enter Upstream.
Upsteam’s centralized cloud-based automotive cybersecurity platform can protect connected fleets from the above threat, even fleets that are already on the road today. Upstream’s solution connects to data feeds and the operational data center infrastructure – the most strategic location for true protection. This creates a demarcation point between the operational network (OT) and information network (IT). Upstream’s solution collects and inspects data from the telematics network and detects threats that target the protocol and application layer in a non-intrusive, friction-less manner. By looking at source and destination addresses, malformed command syntax, illegal commands, injection attacks and unauthorized network sources, Upstream can detect impersonated servers, generate an alert and activate a preconfigured workflow to even prevent the threat. Since the solution is cloud-based, non-intrusive and does not require any in-vehicle integration, it can even protect connected fleets that are already on the road today.
In Summary
The security of telematics data channels should not be overlooked. Like any other critical business data, it should be protected with a comprehensive security platform which is able to piece together every piece of the security puzzle in one central location.
Learn more at upstream.auto

