

Securing Smart Mobility Requires a Fresh Approach to API Security
Connected vehicles and smart mobility services use numerous APIs. Everything from OEM-driven companion apps, infotainment systems, OTA servers, telematics servers, and EV charging management or billing apps rely heavily on APIs to achieve core functionalities. These APIs unlock data-driven services and advanced features, providing new revenue opportunities for automotive stakeholders as smart mobility consumerization evolves.
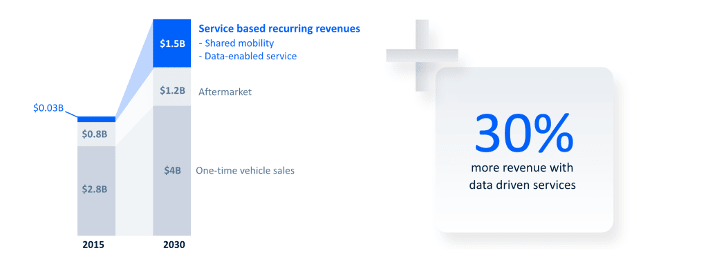
Based on McKinsey’s analysis, OEM revenue growth is significantly driven by recurring services. These innovative revenue streams are expected to increase OEM revenue by 30 percent over the next decade.
But APIs also present significant and fleet-wide attack surfaces, resulting in a wide range of cyber attacks, including theft of personal information, such as banking and social security numbers, or fatal collisions caused by hackers remotely seizing control of moving vehicles.
APIs make hacking so much easier, requiring relatively low technical expertise, and can be done remotely without any special hardware. Despite OEMs implementing advanced IT cybersecurity protections, automotive API-based attacks have become increasingly common. According to Upstream’s 2022 Automotive Cybersecurity Report, during 2021 API-driven attacks accounted for 2% of incidents. But when examining reported incidents since the beginning of 2022, API-driven attacks have tripled and account for 6% of total incidents.
Upstream’s automotive cyber threat intelligence analysts recently discovered (and thwarted in real-time) a VIN spray attack on over 80 connected vehicles that went unnoticed by a well-known IT-based API security solution. A hacker sent pairing request phishing messages disguised as security updates through the OEM’s API, which gave them access to consumer data and remote control functions of vehicles that had approved malicious pairing requests.
IT vs. OT: Smart mobility assets and APIs must be contextualized
How does an IT API security solution miss an event like the VIN spray attack described above?
Due to a lack of context and a lack of understanding of how vehicles operate, IT-based solutions are unable to handle the scope and magnitude of vehicle attacks.
From a cybersecurity perspective, API calls may appear to have the right structure and even the required authorizations, but still indicate an attack. For example, a command to “unlock” multiple cars from the same IP address, a command to “unlock” a vehicle from a different continent, or a command to “roll down a window” while the vehicle is in motion.
IT-based security solutions only deal with isolated API transactions and focus primarily on permissions, volumes, values, and payload correctness — they don’t keep a state of connections, or contextual information about the vehicle itself.
To identify a problem in the smart mobility ecosystem, you need to correlate between the manipulated API and the actual vehicle on the road. For example, the relationship between the origin IP and the vehicle’s geolocation and physical state.
API security requires a holistic view of API traffic and the state of vehicles, applications, and consumers:
- App location and device
- User and vehicle identification
- Vehicle location and proximity to app
- Vehicle state and telematics
- Vehicle data — billing information, service/feature history, manufacturing data, etc.
- State of logins — history of who connected to it and from where
- API call misconfigurations
- Anomalies in API behavior
- A view of fleet-wide API transactions
- Charging station and vehicle API transactions
For API security solutions to be effective, they must be purpose-built specifically for automotive and smart mobility applications and contextualize vehicle data to help the vSOC (vehicle SOC) team understand how APIs are used and whether they pose a cyber or fraud risk.
Rethink API cybersecurity strategies to maximize the value of digital services and features
APIs play a crucial role in the smart mobility revolution. As a result, they have become the top target for attacks, making API security a must-have for OEMs. As bad actors refine their tactics and techniques, threats become harder to detect. To successfully detect and mitigate against sophisticated API attacks, mobility APIs need to be secured in the context of connected vehicles on the road in real time.
But API security can be challenging even in the right context. Once you recognize an issue, you have limited options for responding.What can you do to block it? Is it possible to revoke the token? How do you deal with fraud and data theft? Is user notification possible? It’s hard for VSOC operators to handle such tasks with IT-based API security solutions.
It is crucial to rethink API cybersecurity strategies to maximize connected vehicle services. Automotive stakeholders need to address API-based cybersecurity events in real time and develop technical capabilities for automated resolution.
Upstream is disrupting the market with a unique API security solution, purpose-built to monitor and protect smart mobility applications. Based on digital twins of vehicles, applications and consumers, Upstream layers automotive and cyber expertise to monitor and secure mobility APIs from cybersecurity vulnerabilities, attacks, misconfigurations, and design flaws. This solution seamlessly integrates with Upstream’s cybersecurity platform and managed VSOC to ensure smart mobility stakeholders can deliver a holistic protection against cyber threats.

